Apple's secret OS and the Secure Enclave Processor
Did you know Apple Silicon Macs run more than one operating system at once in order to function.... and this secretive secondary operating system is why you can't upgrade your SSDs on Apple Silicon Macs? But that's not the whole story.
Apple silicon macs and also T2-equipped Macs, iPhones, iPads, and even the Apple watch use a dedicated hardware component known as the secure enclave, and it's more than just marketing.
The secure enclave is a separate processor explicitly designed to handle sensitive operations related to security and privacy.
One of the main operations for the secure enclave is to generate and store encryption keys and biometric data like Touch ID, and it needs to protect this data from various attacks like physical tampering and side-channel attacks. In order to do this, it needs it has its own memory and storage and needs to be isolated from the rest of the system.
To do this all, it also needs its own stripped-down operating system, known as Secure Enclave OS or SEPOS, and can only be accessed by the computer via a few protected APIs.

When a user's password is set up on an Apple Silicon Mac, the password is passed through a one-way hashing algorithm that produces a key used to encrypt the Secure enclave's key. This means that even if someone has access to the password, they cannot access the encryption keys stored in the Secure enclave without the Secure enclave's cooperation.
This is important. This means any encrypted data must pass through the Secure enclave. The operating system and user never get to see this encryption key and can only use APIs to interact with the Secure Enclave.
It also uses a unique identifier, a Root Cryptographic Key, called the Secure Enclave ID, which is used to identify the device. This is fused to the secure enclave during manufacturing without even Apple's ability to access it. This ensures that the encryption keys stored in the Secure enclave can only be used on the device they were generated on.
So if you stole the physical NAND memory modules out of a MacBook and even had the encryption keys, It would not work because you would still need to match the encryption key to the Secure Enclave ID.
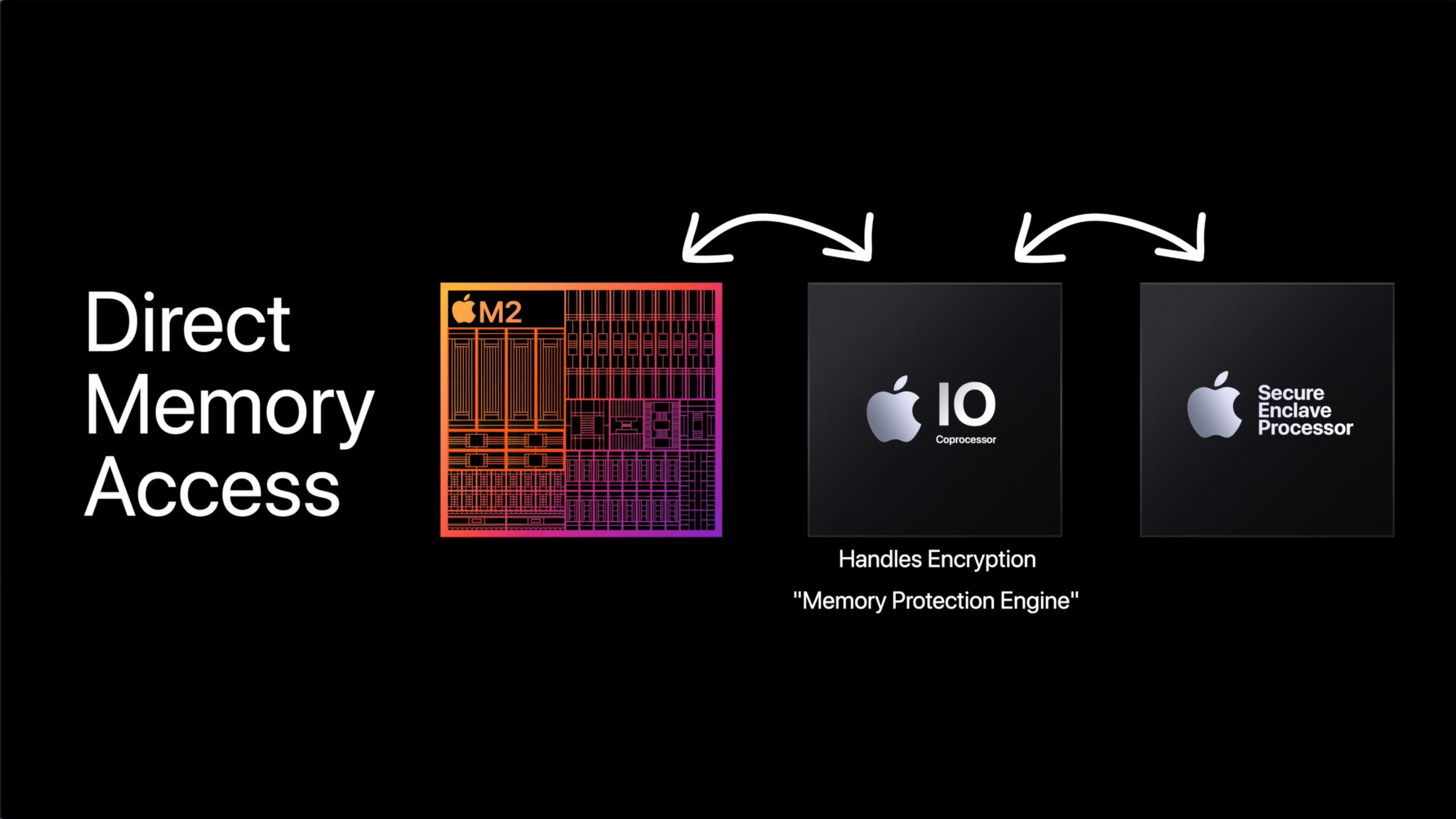
It also helps thwart DMA attacks, where an attacker uses a device with direct memory access, like a Thunderbolt device. A Thunderbolt device uses a PCIe interconnect, and one of the main selling points of PCIe is direct memory access. macOS encrypts its memory and uses an I/O processor that manages communication between the main processor and Secure the Enclave. The memory needs to be encrypted and decrypted, and any device trying to attack memory will only get encrypted data. Apple refers to this as the Memory Protection Engine.
Handling these tasks is SEPOS. The SEPOS is designed to be resistant to attacks, including physical tampering, and it has been certified under the Common Criteria security standard. It's based on the L4 Microkernel, which is popular for a secure embedded system as it has a minimal set of services and uses a highly privileged mode that is isolated from user-level code. This starts to get abstract, but the point is that there's a well-defined interface, and the kernel is small and focused. Thus, it is easy to analyze and verify by security analysts and has a design that allows for specialized isolated subsystems. Apple took this operating system and modified it for use in the secure enclave.
This isn't everything that the secure enclave does, as it does quite a bit, like true random number generation, Secure Neural Engine, AES Engine, Secure Enclave Boot ROM, Secure Enclave Boot Monitor, and so on. I really suggest reading the Apple document on this. It's what I used to make this video.
The end result is if you buy a used Apple Silicon Mac, and the user doesn't provide the firmware password, then there's no way for you to reset it.
SSDs and the Secure Enclave

SSDs generally consist of a controller, NAND memory modules, DRAM cache (found on quality SSDs), and an interface.
Apple's Secure Enclave is tightly integrated for Apple, and the SSD controller itself resides within Apple Silicon. As we previously discussed, the secure enclave generates a hardware encryption key and is used to encrypt the contents of the NAND memory (storage). The key is stored in the Secure enclave, and the keys are derived from a combination of the secure enclave ID and characteristics of the NAND. When a new SSD is installed, it would have to generate a new key. If an attacker might be able to determine the original key by comparing the new key to the old key and identifying the differences between the two. If the new key had different characteristics than the old key, this could potentially reveal information about the old key and compromise security. Apple also uses its own implementation of the PCIe and not NVMe protocol, so Apple would have to also harden its security for NVMe.
Now I'm confident Apple could arrive at a solution as Apple's Secure enclave has gone through multiple iterations now, with roughly 16 versions now at the time of making this video. Apple could arrive at giving users the ability to change NVMe SSDs requiring reduced security settings or perhaps an unlock that warns a user about the potential encryption key exposure.
Secure Enclave is extremely powerful when it comes to security. In my OpenCore Explained video, I broke down Apple's many security innovations on the operating system side.
I consider myself an informed user and I would gladly accept any risk for removable storage over being locked into zero upgrades as the NAND memory, which makes an SSD, has a finite shelf life. A memory cell on an SSD can only be written and overwritten so many times before it fails. SSD controllers identify bad blocks eventually they hit a critical mass and will fail. Apple preventing anyone from swapping these means that every Apple Silicon Mac has a time bomb built into it, and there's nothing end users can do to fix it.
Despite the greenwash marketing, Apple has no qualms about generating eWaste. Also, Apple shipping bottom-tier Macs in RAM-starved configurations and with laughably small SSDs means that the OS will have to use the SSD for memory swap operations when the RAM is completely filled more frequently and with fewer bytes to rotate on very small SSDs like 256 GB. This also shortens the NAND shelf life.
Apple chooses not to tackle this on any front as it knows that it generates money no matter how this plays out: A user has to pay upfront the Apple tax on overpriced upgrades and also has to deal with planned obsolescence baked into the hardware and software. Let's not forget Apple will stop supporting its Mac at some point. It gets to hide behind security as a smokescreen.
So when you see right to repair legislation pop up, please support it. Apple makes wonderful products marred by their disdain for the users who use them.